Iran's Pre-Positioned cyber arsenal: Six-Month infrastructure buildup reveals new threat model
Iranian state actors spent six months building resilient cyber infrastructure using US shell companies, designed to survive military retaliation durin
Iran-Backed hackers target medical giant Stryker with devastating wiper attack
Iran-backed hackers deploy destructive wiper malware against medical giant Stryker, forcing evacuation of 5,000 Irish workers and threatening global h
AI-Powered cyberattack on Mexican government agencies exposes new era of sophisticated threats
Mexican government agencies fell victim to AI-powered cyberattacks using ChatGPT and Claude, exposing citizen data and highlighting new era of AI-enabled threats.
Nordstrom's email system exploited in sophisticated cryptocurrency scam campaign
Cybercriminals exploited Nordstrom's legitimate email infrastructure to send cryptocurrency scam messages disguised as St. Patrick's Day promotions.
North korean apts weaponize AI to supercharge IT worker infiltration scams
North Korean APTs are using AI tools like deepfakes and automated communications to enhance IT worker infiltration scams, making them harder to detect.
Tycoon 2FA phishing empire crumbles: Europol takes down MFA-Bypassing criminal platform
International law enforcement dismantles Tycoon 2FA, a sophisticated phishing platform that helped cybercriminals bypass multi-factor authentication protections.
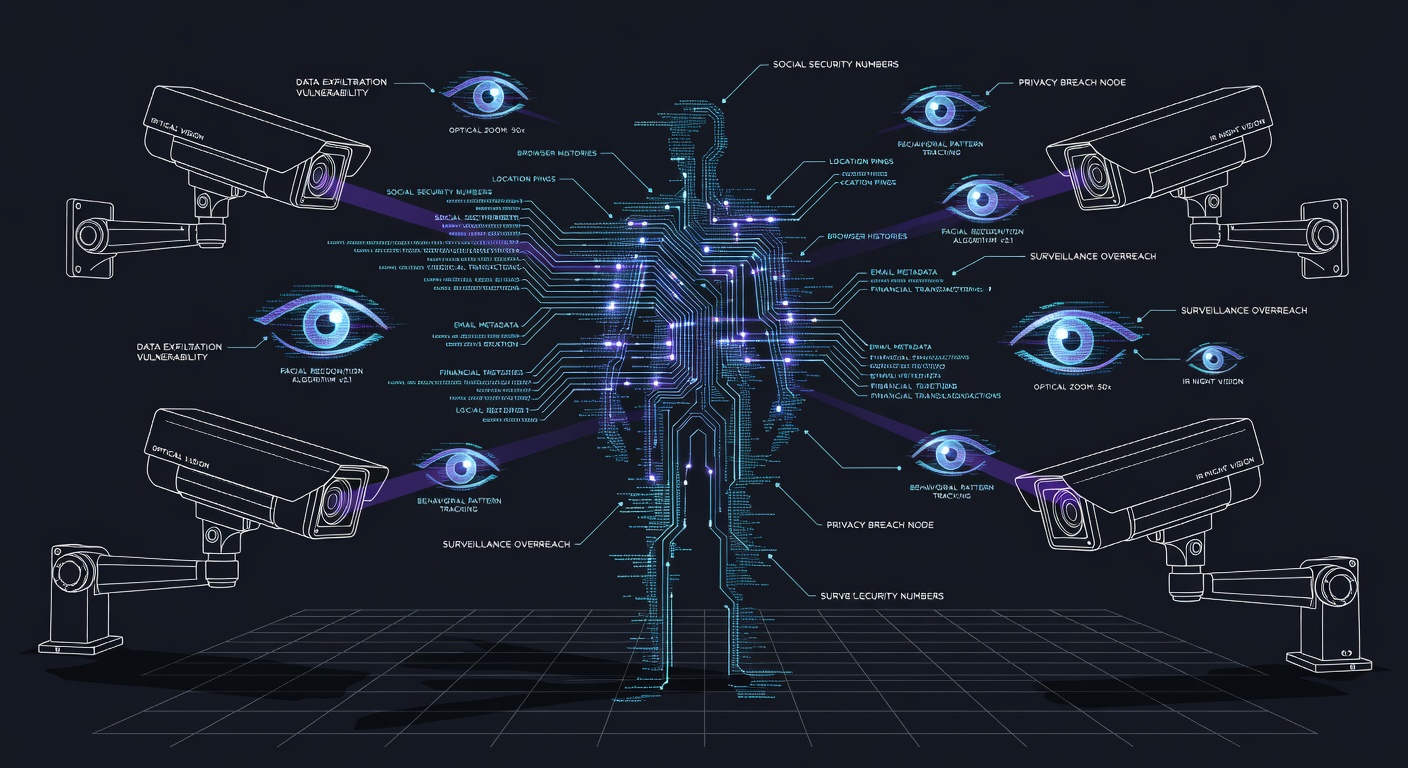
Trump administration's commercial spyware policy reversal sparks security and privacy concerns
Trump administration reverses commercial spyware restrictions, rescinding sanctions on vendors like NSO Group and creating uncertainty about surveilla
Six new android malware families launch sophisticated assault on mobile banking and crypto security
Six sophisticated Android malware families target PIX payments, banking apps, and crypto wallets with advanced capabilities including real-time fraud and data theft.
Chinese nexus actors pivot to Qatar targeting amid middle east tensions
Chinese state-sponsored hackers pivot to target Qatar amid Middle East tensions, demonstrating rapid operational agility in response to geopolitical events.
AI assistants create new security blind spots as autonomous agents gain system access
Autonomous AI agents with system access create new security challenges, blurring lines between data and code while introducing novel attack vectors or
Cisco patches 48 firewall vulnerabilities including two critical 10/10 CVSS flaws
Cisco patches 48 firewall vulnerabilities including two critical 10.0 CVSS flaws affecting edge security appliances, urging immediate updates.
Iran's Cyber-Kinetic war doctrine takes shape: Hacking cameras to plan missile strikes
Iran integrates cyber operations with kinetic warfare by hacking IP cameras for missile strike reconnaissance, blurring traditional warfare boundaries.