Background and Context
The Trump administration has begun reversing years of restrictions on commercial spyware vendors, rescinding sanctions and reactivating contracts that had been frozen under previous administrations. This policy shift marks a significant departure from the Biden administration's hardline stance against companies like NSO Group, whose Pegasus spyware was implicated in targeting journalists, activists, and political dissidents worldwide.
The reversal comes after years of documented abuse by commercial spyware vendors. In 2021, the Pegasus Project investigation revealed that NSO Group's surveillance tool had been used to target over 50,000 phone numbers belonging to journalists, human rights defenders, and government officials across multiple countries. This led to NSO Group being placed on the Commerce Department's Entity List, effectively restricting US companies from doing business with the Israeli firm.
Under the Biden administration, executive orders specifically targeted commercial spyware vendors, citing their role in enabling human rights abuses and undermining democratic institutions. The policy framework established clear restrictions on government procurement and use of commercial surveillance tools that lacked proper oversight mechanisms.
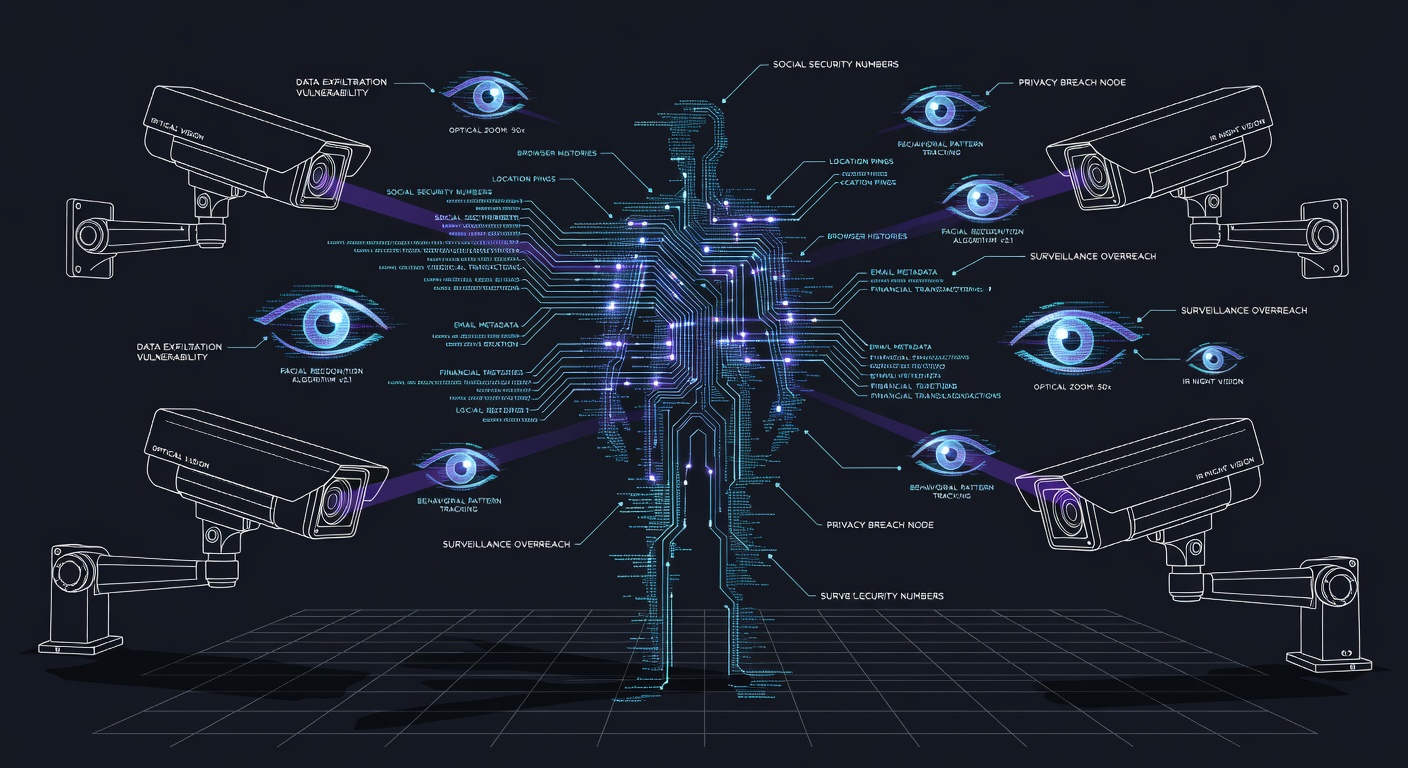
Technical Details and Capabilities
Commercial spyware platforms like Pegasus represent sophisticated surveillance capabilities that exploit zero-day vulnerabilities in mobile devices. These tools can infiltrate iOS and Android devices through various attack vectors, including SMS messages, iMessage exploits, and malicious applications. Once installed, they provide comprehensive access to device data, including messages, calls, location data, and camera/microphone functionality.
The technology operates at a level that makes detection extremely difficult for average users. Unlike traditional malware, commercial spyware is designed to remain invisible while maintaining persistent access to target devices. Advanced platforms can survive device reboots and operating system updates, making them particularly valuable for long-term surveillance operations.
These tools are classified as "dual-use" technology under export control regulations, meaning they have both legitimate security applications and potential for misuse. The sophisticated nature of these platforms means they often rely on previously unknown vulnerabilities, creating broader security risks for all users of affected platforms.
Impact Assessment
The policy reversal affects multiple stakeholder groups with varying degrees of severity. Government agencies, particularly within the intelligence community and federal law enforcement, stand to benefit from renewed access to commercial surveillance tools. However, this comes at the cost of accountability and oversight mechanisms that were previously in place.
Civil society organizations face the most significant risks. Journalists, human rights defenders, and political activists have historically been primary targets of commercial spyware abuse. The Citizen Lab at the University of Toronto has documented numerous cases where these tools were used to silence critics and monitor opposition figures in countries with poor human rights records.
International implications are equally concerning. Allied nations that had aligned with previous US restrictions on commercial spyware may face pressure to reconsider their own policies. This could lead to a global escalation in surveillance capabilities, with authoritarian regimes feeling emboldened to expand their use of commercial spyware against domestic and international targets.
The cybersecurity industry itself faces uncertainty regarding compliance requirements. Defense contractors and technology companies that had adjusted their operations to comply with previous restrictions now find themselves in a regulatory gray area, unsure of what constitutes acceptable business practices.
How to Protect Yourself
For Individual Users:
- Keep devices updated with the latest security patches, as commercial spyware often exploits known vulnerabilities
- Enable automatic updates for both operating systems and applications
- Use reputable mobile security applications that can detect suspicious behavior
- Regularly restart devices, as some spyware variants cannot survive reboots
- Be cautious of unexpected text messages, especially those containing links or asking you to download applications
- Monitor device performance for unusual battery drain, overheating, or slow performance that could indicate compromise
For Organizations and Activists:
- Implement comprehensive mobile device management policies
- Use encrypted communication applications with strong security reputations
- Regularly audit devices for signs of compromise using specialized detection tools
- Establish protocols for handling suspected device compromise
- Consider using separate devices for sensitive communications
- Work with cybersecurity professionals to assess organizational risk
For Journalists and High-Risk Individuals:
- Use burner devices for sensitive communications and investigations
- Implement operational security practices that assume device compromise
- Regularly consult with organizations like the Freedom of the Press Foundation for security guidance
- Consider using specialized secure communication tools designed for high-risk environments
Policy Uncertainty and Future Implications
The current policy shift creates significant uncertainty about the boundaries of acceptable commercial spyware use. Without clear guidelines, government agencies, contractors, and oversight bodies lack the framework necessary to ensure responsible deployment of these powerful surveillance tools.
This uncertainty extends to international relationships, as allied nations that had coordinated their commercial spyware policies with previous US positions now face questions about whether to maintain their restrictions. The potential for surveillance escalation could undermine diplomatic relationships and create new tensions within international security partnerships.
The commercial spyware industry itself may interpret this policy shift as validation of their business models, potentially leading to increased development and marketing of surveillance capabilities. This could accelerate the global proliferation of sophisticated surveillance tools, making them more accessible to both legitimate security agencies and malicious actors.
Congressional oversight will likely play a key role in determining how these policies evolve. Lawmakers from both parties have previously expressed concerns about commercial spyware abuse, and the policy reversal may prompt new legislative efforts to establish clearer boundaries and accountability mechanisms.