AI-Powered Cyberattack on Mexican Government Agencies Exposes New Era of Sophisticated Threats
By NewsNukem Cybersecurity Team | Published Today
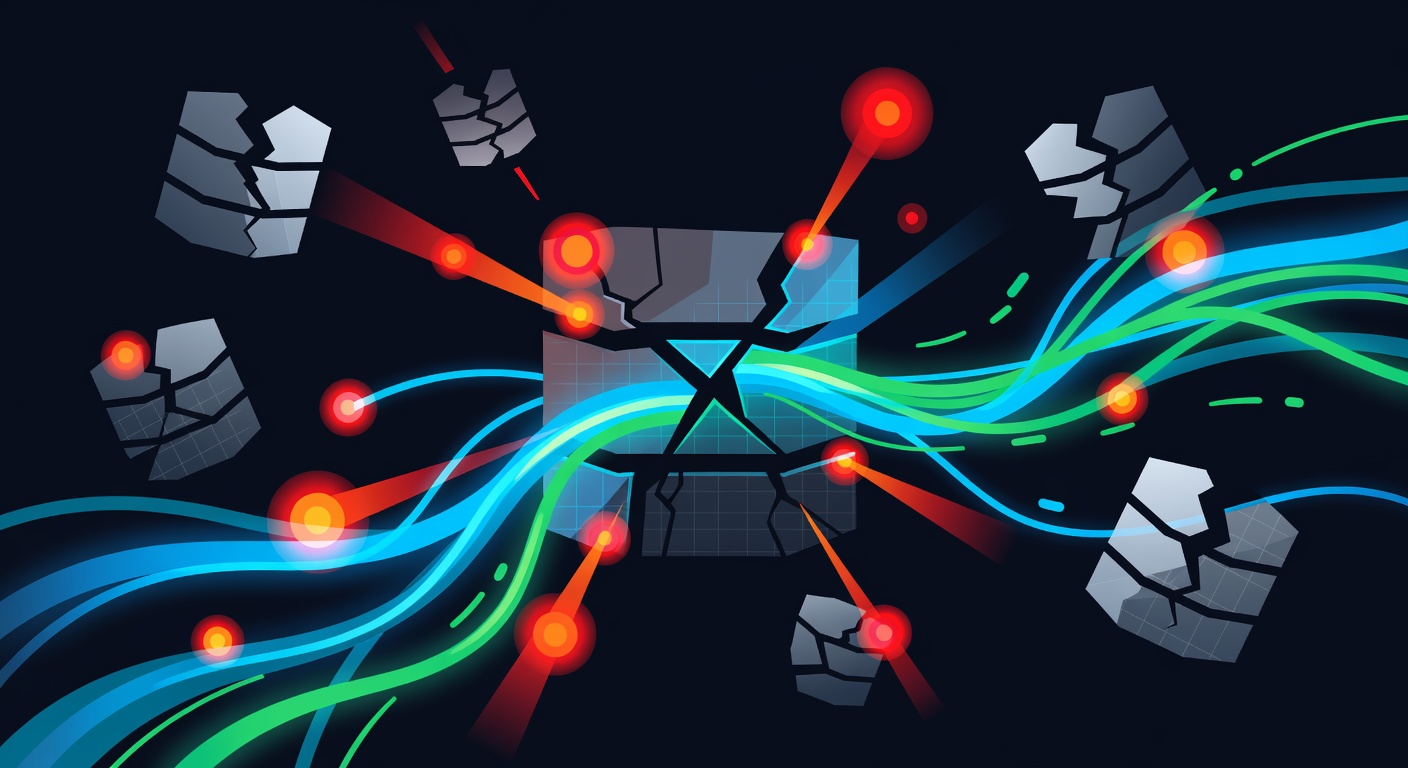
A sophisticated cyberattack on multiple Mexican government agencies has unveiled a chilling new reality in cybersecurity: the weaponization of artificial intelligence tools to conduct large-scale data breaches. According to recent reports, attackers successfully leveraged popular AI platforms including Anthropic's Claude and OpenAI's ChatGPT, combined with detailed playbook prompts, to infiltrate government systems and access sensitive citizen data.
Background: The New AI-Enabled Threat Landscape
This incident represents a significant milestone in the evolution of cyber warfare, demonstrating how readily available AI tools can be weaponized by relatively small groups of attackers to achieve unprecedented scale and sophistication. The attack on Mexico's government infrastructure highlights a critical vulnerability in our increasingly AI-dependent world: the dual-use nature of artificial intelligence technologies.
The attackers reportedly used a systematic approach, employing AI language models to generate attack vectors, craft social engineering messages, and automate various stages of their infiltration process. This method allowed a "handful" of cybercriminals to execute operations that would traditionally require larger, more technically skilled teams.
Technical Analysis: How AI Amplified the Attack
The technical methodology employed in this attack reveals several concerning trends in modern cybercrime. The attackers utilized large language models (LLMs) in multiple capacities:
Automated Reconnaissance
AI models were used to gather and analyze open-source intelligence about Mexican government systems, personnel, and infrastructure. The models could process vast amounts of publicly available information to identify potential vulnerabilities and entry points.
Social Engineering Enhancement
ChatGPT and Claude were reportedly employed to craft highly convincing phishing emails and social engineering attacks tailored to specific government employees. The AI's natural language capabilities enabled the creation of contextually appropriate messages that bypassed traditional security awareness training.
Code Generation and Exploitation
The attackers used AI to generate malicious code, automate vulnerability scanning, and develop custom exploits. This significantly reduced the technical barrier to entry and accelerated the attack timeline.
Operational Scaling
Perhaps most concerning, the AI tools enabled the attackers to simultaneously target multiple agencies and manage complex, multi-vector attacks that would typically overwhelm human operators.
Real-World Impact: Beyond Data Theft
The implications of this attack extend far beyond the immediate data breach. The successful infiltration of Mexican government systems has several cascading effects:
Citizen Privacy Compromised
Sensitive personal data of Mexican citizens, potentially including national identification numbers, tax records, and other government-held information, has been exposed. This creates long-term risks of identity theft and fraud for affected individuals.
National Security Implications
Government agency breaches can expose classified information, diplomatic communications, and strategic planning documents, potentially compromising Mexico's national security interests.
Erosion of Public Trust
Such high-profile government data breaches undermine citizen confidence in their government's ability to protect sensitive information, potentially affecting everything from tax compliance to census participation.
Economic Consequences
The costs associated with breach response, system remediation, legal consequences, and potential regulatory fines can strain government budgets and divert resources from public services.
Precedent Setting
This attack serves as a proof-of-concept for other malicious actors, potentially inspiring copycat attacks against other governments and organizations worldwide.
The Broader AI Security Challenge
This incident illuminates a fundamental challenge in AI governance: how to harness the benefits of artificial intelligence while preventing its misuse. The same capabilities that make AI valuable for legitimate research, business operations, and innovation can be weaponized by bad actors.
Current AI safety measures, including content filtering and usage policies, appear insufficient to prevent determined attackers from leveraging these tools for malicious purposes. The attack demonstrates that even with guardrails in place, creative prompt engineering can often circumvent intended limitations.
How to Protect Yourself
While individuals cannot directly prevent nation-state or sophisticated cyberattacks, there are crucial steps you can take to protect your personal data and digital security:
Use a Reliable VPN Service
A virtual private network (VPN) is essential for protecting your online activities from surveillance and interception. Services like hide.me provide robust encryption and privacy protection, making it significantly harder for attackers to monitor your internet traffic or determine your real location. This is particularly important when accessing government services or conducting sensitive online activities.
Enable Multi-Factor Authentication
Implement MFA on all accounts, especially those containing sensitive information. Even if passwords are compromised, additional authentication factors provide crucial protection.
Regular Security Updates
Keep all devices, operating systems, and applications updated with the latest security patches. Many attacks exploit known vulnerabilities that have available fixes.
Email Security Vigilance
Be extremely cautious with unexpected emails, even those that appear to come from government agencies. AI-generated phishing attacks are becoming increasingly sophisticated and difficult to detect.
Data Minimization
Limit the amount of personal information you share online and with government services to only what is absolutely necessary.
Monitor Your Accounts
Regularly check bank statements, credit reports, and government account activity for suspicious transactions or changes.