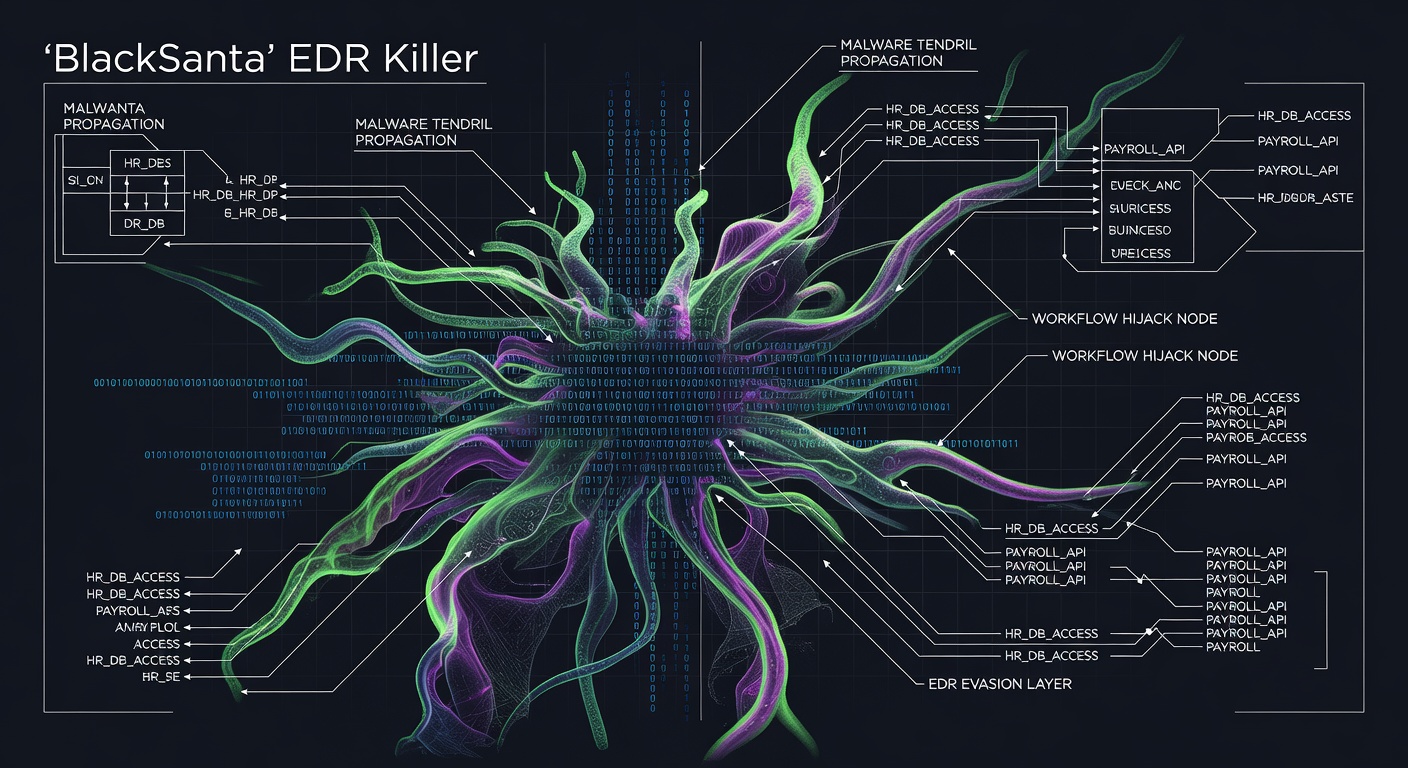
Russian-speaking cybercriminals have launched a sophisticated campaign dubbed 'BlackSanta' that exploits HR workflows to deliver endpoint detection and response (EDR) evasion malware, enabling undetected data theft across targeted organizations.
The campaign represents a significant evolution in attack methodology, with threat actors hijacking legitimate HR processes to distribute malware designed specifically to bypass modern security controls. By embedding malicious payloads within routine HR communications and workflows, attackers are exploiting the trust employees place in internal business processes.
Security researchers have identified the malware's primary capability as neutralizing EDR solutions, which are critical components of enterprise cybersecurity infrastructure. Once deployed, BlackSanta creates blind spots in security monitoring, allowing attackers to operate undetected while exfiltrating sensitive data.
The targeting of HR workflows is particularly concerning given these departments' access to employee personal information, payroll data, and organizational structures. HR systems often serve as entry points to broader corporate networks, making them attractive targets for threat actors seeking to establish persistent access.
The Russian-speaking origin of the campaign aligns with broader geopolitical tensions and the ongoing trend of state-sponsored or state-affiliated groups targeting Western organizations. This geographical attribution suggests potential connections to established threat groups with proven capabilities in developing sophisticated evasion techniques.
Organizations should immediately review their HR security protocols and implement additional monitoring for unusual activities within HR workflows. Security teams must also evaluate their EDR solutions' resilience against evasion techniques and consider implementing layered defense strategies.
The BlackSanta campaign underscores the evolving threat landscape where attackers increasingly target trusted business processes rather than relying solely on traditional phishing or malware distribution methods. This shift requires organizations to reassess their security assumptions about internal workflows and implement zero-trust principles across all business functions.